HIPAA security incidents are attempts to access, use, disclose, modify, or destruct Protected Health Information, or interfere systems maintaining Protected Health Information, that are conducted – successfully or not – by unauthorized persons.
Even when they are not successful, the HIPAA Security Rule requires covered entities and business associates to implement policies and procedures to address HIPAA security incidents in order to comply with the Security Incident Procedures standard of the HIPAA Security Rule.
In most cases, this means organizations must implement policies and procedures to address three types of HIPAA security incidents – those which are blocked by network defenses, those which are detected within the network before Protected Health Information is used or disclosed impermissibly, and those which evade detection and result in a data breach.
Blocked HIPAA Security Incidents
There are many different types of network defenses that can block HIPAA security incidents. These range in sophistication from email protection systems that automatically greylist spam emails, to SIEM systems and Next Generation Firewalls with integrated Intrusion Prevention Systems.
In order to monitor blocked HIPAA security incidents, HIPAA covered entities and business associates should implement network defenses with reporting capabilities in order to identify increasing trends in (for example) spam email, failed login attempts, and other unauthorized access attempts.
This information can be reviewed to establish if it is necessary to implement additional network defenses, reconfigure existing network defenses, or strengthen access controls (i.e., by adding multi factor authentication) to better safeguard the confidentiality, integrity, and availability of Protected Health Information and the systems on which it is created, received, stored, or transmitted.
Detected HIPAA Security Incidents
Detected HIPAA security incidents are those which are not blocked by a network defense, but which are identified once they are within an organization’s network. Examples include phishing emails that are identified by end users before they interact with them, and malware identified by anti-virus software.
In these cases, it is necessary for covered entities and business associates to develop policies for reporting HIPAA security incidents, monitoring other end user’s inboxes and devices, and reviewing how unsuccessful HIPAA security incidents were able to avoid detection by network defenses.
In the event that (for example) a phishing email evaded detection by an email protection system, and a risk assessment identifies a likelihood it could happen again, it may be necessary to increase the amount of HIPAA security awareness training being provided to all members of the workforce – including the procedures for reporting suspected HIPAA security incidents.
Successful Incidents and HIPAA Data Breaches
When an attempt to access, use, disclose, modify, or destruct Protected Health Information is successful, covered entities and business associates must have policies and procedures in place to respond to the incident. At a minimum, the policies and procedures must cover:
Incident Identification & Reporting – A process for detecting and reporting successful HIPAA security incidents including unauthorized access, software anomalies, and system failures.
Assessment & Prioritization – Procedures for assessing the scope and potential impact of each incident to prioritize responses when multiple incidents are reported simultaneously.
Containment & Recovery – Corrective measures for each type of incident to contain the incident, minimize harm, cleanse affected systems, test the systems and restore security.
Investigation & Documentation – Procedures for investigating how each incident occurred and documenting what actions were taken at each step of the HIPAA security incident response.
Notification & Compliance – If required, notify law enforcement agencies, affected individuals, regulatory authorities, the media, and upstream covered entities or business associates.
Policy Review & Improvement – Regularly review the policies and procedures and update when necessary, based on investigation outcomes, to improve response procedures.
Incidents Attributable to Insiders
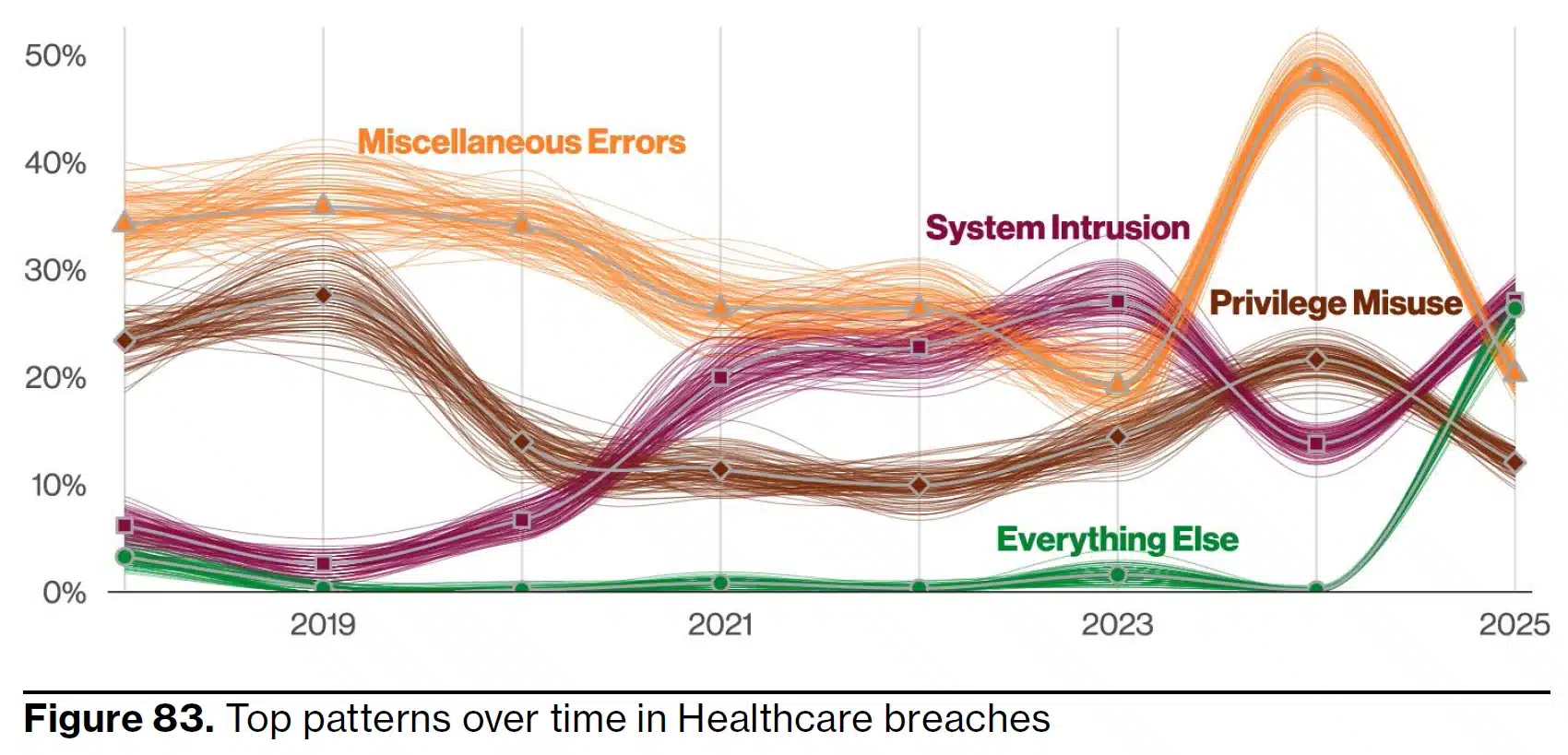
When developing and implementing policies and procedures for responding to successful incidents and HIPAA data breaches, it is important not to overlook the threat from malicious insiders. The misuse of login credentials to impermissibly access, use, or disclose Protected Health Information accounts for 16% of data breaches in the healthcare industry.
Furthermore, organizations that fail to consider the threat from malicious insiders can pay heavily for the oversights. In 2024, HHS’ Office for Civil Rights fined a pain management medical practice $1.19 million for compliance failings that resulted in a workforce members fraudulently generating 6,500 Medicare claims using Protected Health Information maintained in the practice’s database.
HHS’ Office for Civil Rights has published guidance on what the HIPAA Security Rule requires covered entities and business associates to do to comply with the Security Incidents Procedures standard. Organizations that require further advice are advised to seek independent compliance advice.
Image credit: Looker_Studio ©AdobeStock / ©Verizon / ©defensorum




